Yubikey is a curiosity-driven side project for us and we have plans to dig a bit further into hardware as time permits. If anybody could confidentially help with NXP datasheets, it would be much appreciated.
Yubikey Neo is a $50 authentication token (with bells and whistles) from Yubico. Yubico advertizes it as "practically indestructible". The product security section also claims that the device comes in a "tamper-proof casing" that is "practically impossible to tamper". Having previously seen similar claims, we decided to put a Yubikey Neo to the test and at the same time take a peek at how the device was designed.
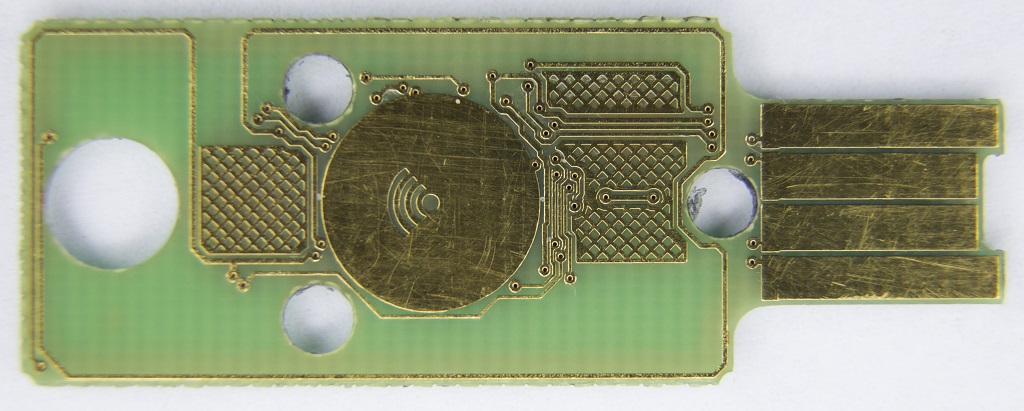
Many vendors go long ways to ensure physical security of their devices. Chemical-resistant epoxy compounds, capacitive sensors, temperature sensors, light sensors are among popular choices. Yubikey choice: some standard pressure molding polyamide (or whatever it is) plastic that is easily dissolvable in acetone. So, we gave a brand new Neo an acetone bath, and after about 30 minutes of stirring, a perfectly clean PCB was fished out. Since no internal components were reactive to acetone, the board was in perfect working condition. On the bottom of the container, after milky-gray acetone solution settled down, we discovered a layer of white powdery substance which is a fiber reinforcement material added to the plastic to improve its rigidity.
Contrary to Yubico's claims, Yubikey appears to be quite destructible. Do not push on it when you touch the sensor while the key is plugged in to a USB port. The point where it bends the most happens to be the point where USB vias are located and through which NFC antenna loop goes. To make things worse, the injection molding hole right next to the connector makes this area even more susceptible to bending.
It is also not recommended to attach a Yubikey to a key ring. The ring hole sits dangerously close to the edge of the PCB. The NFC antenna loop passes between the hole and the edge. Considering that Yubico-chosen plastic is easily scratchable, it will eventually wear off to the point where NFC antenna could be damaged. You may also want to be gentle when connecting or disconnecting the key. After a few hundred times of plugging it in and out, the plastic will get thinner and the key might start falling out or losing connectivity.
Yubico achieved FIPS140-2 Level 1 certification for its Standard and Nano keys (Level 2 for the design). At the time of writing Yubikey Neo does not appear to be FIPS-certified. That is not a big deal, considering that Levels 1 and 2 of the FIPS140-2 certification are just a marketing gimmick for most electronic devices. For those interested, FIPS140-2 Level 1 means that a device has at least one standard ("approved") security algorithm or function and Level 2 means that physical design is tamper-evident. Considering that, FIPS140-2 certification for the device should be easily achievable.
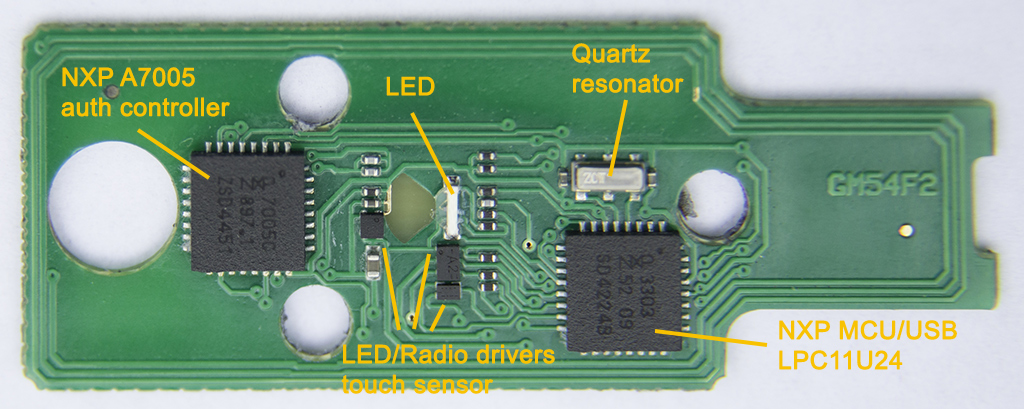
We estimate total manufacturing cost of YubiKey Neo as $6..$8 USD. This breaks down to:
A couple of days after this article was published we received an email from Yubico's CTO Jakob Ehrensvärd. Jakob, in a very polite and unbiased way, in spite of being bombarded with clarification requests that our article must have generated, disputed some of our findings and asked for more details. Below is what we discussed with Jakob in a couple of follow-up emails.
Jakob clarified the "practically indestructible" term as:
"The word "practically" here obviously means "in normal everyday use",
including everyday gizmo dangers, like being soaked in water or being
crushed in a pocket. Destroying the Yubikey is not that hard - a pair
of pliers would make that job easy."
We agree with Jakob's comment that although the device's electronics are easily accessible, it does not mean that the device is insecure or easy to compromise. We still think that there is a difference between the meanings of "tamper-evident" (which Yubikey is) and "tamper-proof" (which Yubico uses to describe Yubikey's enclosure on their website). The latter is not quite accurate. We have not started exploring MCUs and communications protocols, and we do expect YubiKey to get high marks there, but on the physical security side, the device cannot be declared "tamper-proof" when a household solvent provides a trivial way to strip it down to its electronics. We further believe that it might be possible to cut plastic around the edge of the device and through the four holes and just open the key without use of any chemicals. That could allow an attacker to access internal components, add its own electronics for eavesdropping purposes, and assemble the device back, leaving very little evidence of tampering. HexView neither has required craftsmanship skills nor strong desire to test this theory. If anybody is willing -- you may need to dissemble two Yubikeys to put one back together. The plastic casing material also melts well, which might help with sealing the case back together (or just use acetone as a glue).
Jakob agreed with our claim that vias generally should not be located around stress lines. He further commented that because the key's body is rather rigid, applying significant force to a key inserted into a USB port will likely damage the port, not the key. HexView validated and confirmed this claim. So, don't push on the key, it could damage your USB port. Over time, stressing the key repeatedly can still in theory damage the key, but, agreeing with Yubico, the possibility of this should be negligible in real life. HexView still believes that this problem could have been avoided altogether by putting the touch sensor on one or both side edges of the device instead of in the center of it.
Jakob admitted that routing antenna conductors between the key hole and the edge of the device was a design compromise and that applying excessive bending stress to a key ring will damage the antenna and might also break the device further down the board. However, there have been no warranty returns showing this type of damage.
Our claim that plastic around USB connector can wear off over time after multiple insertions was of primary concern to Yubico. Here is how we tested the claim. We dug through a pile of old USB hubs and found two specimens of questionable origin -- one with the tightest fit requiring a bit of force to insert or remove the key and one with the loosest fit. One of the ports on the tighter-fit hub, conveniently, had rather rough metal body. We proceeded by inserting and re-inserting the key a few dozen times to different ports on the hub. A noticeable amount of plastic particles was stripped off the key during this process. We them inserted the key in the looser-fit hub and turned it on its side so that the key faced the ground and it fell right out. HexView understands that such extreme testing methods do not necessarily reflect "real life" use scenarios and may not be a clear indication of deficient design.
It looks like Yubico took criticism well and redesigned the case. The key ring hole is now more robust and Yubikey 5 uses chemical-resistant plastic. Good!
HexView's InfoSec experience goes back to early 2000s. Our company became one of the first (if not the first ever) to adopt "reasonably-responsible" vulnerability disclosure process where vendors were given a fixed timeframe to resolve a problem, and upon expiration, a full public disclosure would be released. Those days were great... The company has since evolved into a boutique that provides higher-level management consulting services, such as reviews of your relationships with security vendors. We also perform security assessments for the Internet of Things and specialized devices, such as medical equipment. Let us know if we can help.